Where Every Risk is an Opportunity

How China is using curiosity of the 'Jasmine Revolution' to spy electronically on democracy supporters—even in India
In March, A couple of weeks after returning from the Pearl River Delta after reporting on China's nascent labour movement, I received an intriguing email from molihuaxingdong2@gmail.com, which translates as 'action Jasmine'. The attached file, 'Best material of Chinese Jasmine Report' with its implied promise of privileged information on dissent in China, seemed too good to pass up. I took the bait. The moment I opened it, I realised I'd made a mistake.
It was malware—software with malicious intent, that is—and the sender's email address turned out to be quite similar to molihuaxingdong@gmail.com that has been used by anonymous Chinese pro-Jasmine bloggers.
Liam O'Murchu in Symantec's Silicon Valley office examined it for me. It was an information-stealing virus disguised as Excel and Word files. "It records keystrokes and extracts stored passwords on your [computer] system along with other system information, and sends that to the attacker; it will also download and execute additional files," he explained. "The command-and-control server is just a staging post that will tell the threat where the real command-and-control server is located."
I wasn't alone. Other activists were also targeted. Anthony Spires is a sociology professor at The Chinese University of Hong Kong. He is also associate director of the Centre for Civil Society Studies, which supports China's labour movement. In March, he received two messages from 'Molihua Xingdong' at a Gmail address. "The first said something about 'wanting to apply to your program', and the second—very cleverly, I thought—said something about 'sorry, I forgot to attach my CV and study plan,'" Spires says. "I deleted them both immediately because they just looked too suspicious. Although they were both signed by someone named 'John Black', the English grammar and syntax mistakes sent up another red flag." Like the email I'd received, Spires also got an EXE file. "Although I wouldn't accept such a 'student' in any programme of mine, I would give him/her/them an A for effort!"
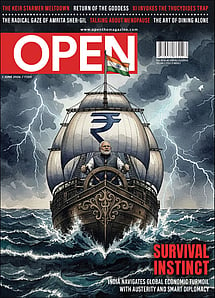
Survival Instinct
22 May 2026 - Vol 04 | Issue 72
India navigates global economic turmoil with austerity and smart diplomacy
After North Africa and the wider Middle East erupted in pro-democracy movements in January, some Chinese intellectuals began organising rallies in public squares. The movement was soon dubbed the Jasmine Revolution. The authorities responded with a severe crackdown on pro-democracy and civil society activists. The highest profile arrestee was Ai Weiwei, a famous artist who helped design the Beijing 'Bird's Nest' Stadium for the 2008 Olympics. He was ostensibly arrested for economic crimes, but many inside China say he was nabbed for advocating democratic reform. Ai's whereabouts are still unknown and official charges are yet to be filed.
Underneath the high-profile crackdown, a more covert war appears to have been waged. And if you examine previous examples of recent Chinese cyber attacks, a clear pattern emerges.
China's most famous cyber attack was uncovered in March 2009. Researchers from the Canada-based Infowar Monitor discovered Ghostnet, a wide-spread network of cyber-espionage that targeted the Dalai Lama and his supporters, even infiltrating the computers of Indian government officials at embassies abroad. Ghostnet wasn't an isolated incident. During Operation Aurora, also unleashed in 2009, Ai Weiwei's bank accounts were compromised.
It's hard to know the extent of China's cyber warfare programme functions, since there is no official acknowledgement of its existence. A spokesperson at the Chinese embassy in London told the BBC that Ghostnet was nothing more than a "propaganda campaign" by the Tibetan Government in Exile.
"Anyone who says [these attacks are] just the State is just wrong," says one of the Ghostnet researchers, Greg Walton, who now runs MetaLab Asia, a cyber intelligence company. "Anyone who says it's just kids is wrong. It's layered. It's rather elegant, I suppose."
The Jasmine assault has what Walton calls similar "social engineering" characteristics. In the past, hackers have used the email address of Human Rights in China head Sharon Hom to send out
and infiltrate computers with spyware, and entrapped Dalai Lama supporters by using his supposed schedule as a bait. In the email I received, the lure was highlights of the Jasmine Revolution. "This," as Hom points out, "is not unique to China-related subject attacks. This is a common breach-of-trust attack." Other attacks have come through fake Facebook pages claiming to support the Jasmine Revolution.
In considering the Jasmine attack, it's instructive to examine the biggest funder of China's movement for civil society: the National Endowment for Democracy (NED). Though it's a private organisation, its funding comes almost entirely from the United States Congress. When Liu Xiabao won the 2010 Nobel Peace Prize, NED congratulated him on its website. The NED funded two organisations that Liu worked for: Democratic China, a magazine, and the Independent Chinese Pen Centre, a writers' group.
The NED is despised by the Communist Party. So it's not surprising that on 5 April, the day before the outgoing US Ambassador Jon Huntsman blasted China for jailing Liu Xiabao and Ai Weiwei, NED staffers received an email claiming to offer some extraordinary footage: 'On Monday, we expressed scepticism at reports suggesting US ambassador Jon Huntsman was present at the Jasmine non-Revolution in Beijing. But Holy Angel Moroni! A video has now surfaced of him standing right outside McDonald's on Wangfujing, the location of the would-be protests, with a pair of shades and a leather jacket sporting the US flag… In the 1:30" clip (see video after the jump), a Chinese man in the crowd calls out to him, "Hey Mr Ambassador, what are you doing here?" Huntsman responds, "I'm just here to look around." The Chinese man asks, "You want to see China in chaos, don't you?"'
There was no video, just a virus.
"I don't think any of our staff fell for it," says Louisa Chiang of NED.
The NED also supports groups like Human Rights in China, China Labour Bulletin and China Labor Watch, one of the groups I reported on while in China. In fact, in their Shenzhen office I'd met migrant workers they were organising. I'd also visited injured workers at a hospital, and spoken at length with the group's young staffer, who asked me not to reveal their identities for fear it could compromise their undercover investigations at factories in China.
But the virus seemed to rattle China Labor Watch. "Our computers are fine, thank you very much," the woman answering the phone at the group's New York office said. I called back again and reintroduced myself. She slammed the phone down.
For activists inside mainland China, this fear is warranted. In late March, in the city of Dongguan, I was talking with Chao Wei Yun, a former migrant worker cum labour activist cum amateur lawyer. At the end of an hour-long discussion, our conversation turned to the risk involved in taking up such 'sensitive' issues. Chao was scheduled to meet a colleague around the time of the spring festival in Guangzhou, a neighbouring city. The meeting never took place. "He's now jailed and I couldn't reach him on phone anymore," he explained. "I only know he disappeared. I don't know what actually happened to him." The man led a pro-democracy group on QQ, a Chinese instant messenger service (of a social networking site) with more than 630 million users that is notoriously susceptible to malware. "After he was arrested, two QQ groups have already been shut down."
How do you know you can trust people you meet online? I asked.
"I just trust [them] from what they say online," he told me. "But there's a possibility that there may be spies. I may be arrested one day."
Reporting from China sponsored by the Pulitzer Center on Crisis Reporting