Hack and Run
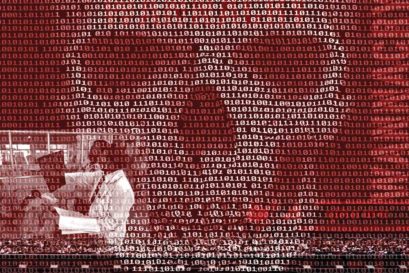
Can India afford to remain unprepared in the face of rising cyber terror?

A DUBIOUS SORT OF ‘social engineering’ is the latest matter of concern for India, just as it is elsewhere. No, it has nothing to do with Mulayam Singh Yadav’s or Mayawati’s politics or, for that matter, the efforts to uplift Mahadalits. In these times of social media influx, crime too has donned virtual shades. Social engineering of the cyber kind is all about a hacker or a cyber criminal befriending an unsuspecting social-media user— a friend or a stranger—to elicit as much information from the potential victim. This data is then used for malafide purposes: to steal money online, extract a ransom or make other demands through coercion. And while most of us may consider ourselves aware and secure, no one is safe.
“The aim of the cyber predator masquerading as a friend could be to harm a person’s reputation, grab money or even to exploit someone sexually,” says Mumbai-based cyber security specialist Ritesh Bhatia, whose company, V4web, offers solutions to fight cyber strikes on the Government as well as the private sector. Cyber crimes, like others, could vary from petty crimes to serious offences, even wars. A recent survey by PricewaterhouseCoopers India and industry body Assocham had put the spotlight on the gravity of the situation: cyber crimes in India rose 350 per cent in three years between 2011 and 2014. They have been growing at 70 per cent or more annually ever since. National Investigation Agency (NIA) Inspector General Alok Mittal has said that one-sixth of cyber crimes reported in India take place on social media. Worse, the National Crime Records Bureau had stated some months ago that the conviction rate for cyber crimes in the country is at an abysmal low of 0.7 per cent.
Bhatia, who handles petty offences and serious economic crimes, was recently approached by the Mumbai Police with a case of harassment of a young man who was, ostensibly, a victim of cyber bullying, one of the most common offences committed online. Someone who knew this young man well posed as a girl with a seemingly real online identity and developed cyber intimacy with him. Many weeks later, ‘she’ asked him to send her a video of himself in the nude. Though he was shocked, he immediately obliged. It turned out to be the worst decision he’d ever taken. What followed were threats to send his nude photos to his fiancée. The intention, the police suspected, could be jealousy or simply to wreck the young man’s wedding plans.
Bhatia easily tracked down the position of the server used for the mischief and the location. What concerned him, though, was the police’s tardiness in response once they had all the information they needed. “You know they are not accustomed to even these basic facets of fighting cyber crime. They expected me to track down the person, which is not my job. It could be the brother or father or the nephew of the owner of the computer, not necessarily him or her. The rest of the operation had to be typical police action. My role was over when I identified the server… This acute lack of awareness is sickening and puts the spotlight on how unprepared many of our forces are,” he says. None other than Mumbai Police chief Datta Padsalgikar conceded recently that his men are poorly equipped to handle such cases. Padsalgikar said the city police lack trained personnel to deal with rising cyber crime.
Before the country gets battle-ready to fight off international hackers with or without state support—cyber crimes that are equivalent to a war—there are small wars to be won, too, to ensure protection from cyber bullying of the kind numerous teenagers and even adults face, and to safeguard an individual’s hard-earned money. Recently, a Delhi-based girl discovered to her dismay an alternative Facebook page of hers, which had a doctored chat with a Hyderabad-based youngster. The intention could have been to blackmail her over the ‘indecent’ things she had reportedly told him through her Facebook private chat option. The young girl was wise enough to alert her parents and browbeat the boy who later confessed that he had done it to win her affection. But solving cases of cyber bullying isn’t all that easy in most cases. (See ‘Cyber Bullies’, 10 June 2016, Open).
HACKERS HAVE SUCCESSFULLY broken into communication networks of high-speed transactions such as ATM withdrawals, in an indication that smart chips, PIN numbers and one-time passwords are not safe anymore. Serge Malenkovich, deputy head, social media, at software security behemoth Kaspersky Lab, says one hoped sometime ago that migration to smart chips from those that had embossed digits and a signature field as protection was good enough. No longer, he argues, outlining how hackers could use devices, even as small and cheap as a Raspberry Pi computer, to retrieve the communication between the bank and the ATM card and try to steal PIN numbers and the Card Verification Value (CVV) codes of credit or debit cards. This happens, according to Malenkovich, thanks to weak encryption, which is meant to ensure data security. After intercepting communication between the card and the bank, cyber criminals can trick the users into revealing their CVV numbers and PIN numbers. If the machine (either at an ATM booth or a petrol station) asks you to re-enter your PIN number claiming an error, or requests a CVV number, the best way to avoid being duped is to cancel the transaction and start anew. “Most bank-related crimes are also insider jobs,” an RBI official says pithily, emphasising that financial institutions and governments must invest “either money for building safeguards or time in training its people to fight the rapidly evolving war on the cyber space”.
There are variants of cyber predators too: Ransomware, a malicious software, for instance, hacks into an individual’s or an organisation’s computer files and blocks them until they pay a fee. In June this year, the University of Calgary in Canada found its emails and files encrypted by attackers. The administration finally took a call to pay the ransomware’s demand of $20,000 in bitcoins to retrieve the data. Similarly, a US hospital in Hollywood had to pay $17,000 in bitcoins to regain access to its data. These sorts of attacks are much more dangerous than others such as phishing, which uses emails (often masquerading as official emails from a fictitious bank) to steal data. The warning that most cyber security experts have for users is to not entertain any such mails or click on unusual links and also to report problems immediately if something is amiss in your system.
Similar are honey pots, which have become a routine affair in airports and train stations across the world when a user logs on to a free wi-fi option. Kevin Mitnick, a former US-based hacker notorious for hacking into 40 major American companies who is now a leading cyber security consultant, has warned against logging on to such free wi-fi networks in public spaces. The keystrokes made by the user of such a fake access point are visible to the hacker who would immediately send an update to the unsuspecting traveller to install. If he or she, who is delighted at the option of using wi-fi after a journey or in transit, installs it, the hacker will get complete access to the user’s computer.
Many cyber pundits have referred to the trend of getting tricked into installing software or believing that a fake email ID is a genuine one as the ‘hypnotising effect’ of the internet. A New Delhi-based ethical hacker says, “Be it an individual handling his email or a corporate executive managing payment-related emails, people don’t take good care to check the email address properly. They are mostly vulnerable to similar sounding, yet fake email IDs.”
For this reason, business-email compromise scams, also referred to as ‘man-in-the-middle attacks’, are a major scourge that corporate India must deal with. “Corporates are the ones to blame for this. They don’t invest enough in protecting their emails and they often spring into action only after a major incident happens. That is my experience in India,” says a US-bred former chief executive of a highly valued Indian conglomerate.
Mumbai-based Bhatia agrees that business-email compromise scams are rampant in India, and he himself works with scores of companies to ensure that spam filters are in place to recognise unusual mails and to train staff in verifying payment-related emails. Hackers typically create similar sounding emails of a manufacturer and even purchase similar looking domains to request money from vendors for prospective delivery of goods.
“I have seen numerous cases of this in India,” notes a cyber security executive based in Delhi without revealing the names of affected companies, citing confidentiality. He also adds that when such large-scale economic offences take place, newspapers tell you that an ‘insider hand’ is often the reason behind the siphoning off of crores of rupees.
Companies also need to protect their data against outages, floods and other man-made as well as natural calamities. According to the recent PwC-Assocham survey, 56 per cent of the firms surveyed in India have increased their spend on internet security compliance programmes and 61 per cent said they would raise their investment in compliance programmes over the next two years.
WHILE INTERNET SECURITY pundits recommend an all-out campaign to further familiarise individuals and corporates with cyber dangers, they stress that the Government, too, must factor in fast-evolving challenges as it goes ahead with its digitisation exercise. Of course, India has taken baby steps to combat the menace at a time when cyber warfare is seen as the fourth arm of defence, after the Army, Air Force and Navy. Though it has come under cyber attack for more than a decade, it was only in 2013 that India passed the National Cyber Security Policy, put forth by the Department of Electronics and Information Technology (DeitY), which has recently been classified as a ministry. A while ago, Vinay Mohan Kwatra, now joint secretary in the PMO, and an expert in counter terrorism and cyber security, had told Open that India was a land of ‘no resistance’ for hackers. “There is none,” he had said, when asked about the country’s cyber security capabilities.
“The situation has not changed much except that there is an awareness of what has to be done. But execution is still taking time,” says a senior Government official close to the matter. True, India has in place a policy, and various agencies, including the CBI, with divisions in place to combat cyber crimes. CBI spokesperson Devpreet Singh, however, didn’t respond to repeated requests from Open about the agency’s anti-cyber crime prowess. Neither did PK Gautam, the point person at CBI for cyber crime activities.
Ajay Kumar, additional secretary, DeitY, spoke about the steps the Government is expected to take to enhance cyber security in the face of attacks on Indian utilities, citizens and private sector enterprises from various corners, especially from China and cyber spying agencies (Read the full interview ). He also talked about an earlier plan to hire ethical hackers the way the US, Israel, Russia and others (including North Korea) do, which could help combat anti-India cyber crime. He also dwelt on public-private partnerships to fight the menace.
Notably, cyber espionage team Danti has access to internal networks in Indian Government organisations, says a Kaspersky report of May 2016. Danti has also created emails in the names of several high-ranking Indian Government officials, the report adds. It points out the loopholes that hackers tap: ‘Kaspersky Lab’s Global Research and Analysis Team has spent the last few months observing a wave of cyber espionage attacks conducted by different groups across the Asia-Pacific (APAC) and Far East regions, all of which share one common feature: in order to infect their victims with malware, the attackers use an exploit for the CVE-2015-2545 vulnerability. This weakness in Microsoft Office software was patched at the end of 2015, but still appears to be of use to these threat actors. The Platinum, APT16, EvilPost, and SPIVY groups were already known to use the exploit, and they are now joined by a fairly new and previously unknown group called Danti.’ CVE-2015-2545 is a feature that makes MS Office programme users easy prey for hackers. This ‘vulnerability’ was discovered in August 2015 when the Platinum group launched attacks on targets in India. The shortcomings were fixed in an MS Office update later. SVCMONDR, like Danti, is another new cyber espionage agency. Danti has also targeted Indian embassies in Denmark, Colombia and Hungary.
True, India’s power grids and various other public utilities are a mix of digital and manual and therefore much less vulnerable to cyber attacks compared with countries that have gone fully digital, especially the US, Singapore, Estonia, Lithuania or even cities such as Dubai. Yet, as India has embarked upon Prime Minister Narendra Modi’s ambitious digital campaign and in making our cities smarter and connected to the grid, the challenges are only going to get worse. In recent years, government entities such as Defence Research Development Organisation, BSNL, PMO website and several other official websites, including MHA, NIA and CBI, have come under attack from overseas cyber ninjas. Cyber attacks were also reported on systems of India’s military forces and those of BARC. The internet security firm PandaLabs says that 2015 saw the greatest number of cyber attacks recorded around the world, with a total of 304 million. It also adds that more than a quarter of all malware samples ever recorded were produced in 2015.
It is dangerous to stay unprepared. Analysts suggest encrypting systems to toughen them and constantly raising awareness about various types of cyber attacks. “Computer Emergency Response Team (CERT) and National Informatics Centre (NIC) will have to play a stellar role in making this happen,” says a senior Government official. These two agencies handle the Centre’s IT infrastructure. Hiring young people to build cyber offensive capabilities is what the country must lay emphasis on, he adds. In fact, such a plan has been launched by the Government at least on a smaller scale though it plans to boost its efforts (24 July 2014, Open). It was Israel that started it, with its Talpiot Unit 8200 programme, by recruiting teen hackers and math wizards, and later China and North Korea followed suit. Pyongyang meticulously hires teenagers for its cyber sweatshops to target overseas companies—the latest being Sony over its backing for the film The Interview, which satirises North Korean communist dictator Kim Jong-un. North Korea also uses its teenaged wunderkinds to gamble online to rake in millions that are reportedly ploughed into its nuclear programme.
Bhatia suggests public-private partnerships to strengthen India’s cyber defence potential. For his part, S Ramadorai, National Skill Development Corporation (NSDC) chairman and former TCS honcho, suggests that the Government of India hire its pool of cyber security talent the way companies such as Facebook and Twitter do. These companies organise ‘bug-bounty programs’ in which hackers are invited to find vulnerabilities in their systems (without causing damage), he says. “On disclosing the flaw, they can be paid to the tune of $10,000. This is a great way to identify talent,” in Ramadorai’s words.
The Government must sit up and listen, and act swiftly. After all, in the murky world of cyber crime, assets are lost and wars won in nanoseconds.













More Columns
Art of Love Nandini Nair
Fruit of the Nation Madhavankutty Pillai
Ladakh: Magic Mountain Abhilasha Ojha